Deep Security is Hybrid cloud security that rapidly defends your cloud network in length and breadth. The main responsibility of deep security is to improve SOC productivity and high security to your cloud. Cloud is the best option to store your data but security matters too and cloud security should be impenetrable. Deep Security gives […]
Do You Know How BIG-IP Actually Works? A load balancer is a device that acts as a reverse proxy and distributes applications or network traffic across a number of servers. Load balancers are used to increase the capacity (concurrent users) and reliability of applications. They improve the overall performance of applications by decreasing the load on servers […]
Hello friends! We have already introduced many blogs on Cisco Identity Service Engine (ISE), in which we already covered multiple topics. If you have not checked those ones, then we recommend you check those blogs. The list of Cisco ISE blogs is mentioned below, you can go through it as per your learning plan. A […]
Many organizations are looking at HCI when looking to augment their IT infrastructure. With every major vendor bringing about “game-changing” innovations into the fray at a rapid pace, this document summarises important criteria to decide which HCI solution to buy. Form Factor (Hardware appliance v/s software), third-party hardware support, Cloud integration, Kubernetes integration, and Analytics […]
Many apps and services rely upon digital certificates to provide authentication and additional security through encryption. You can install and configure Active Directory Certificate Services (AD CS) as the foundation of your public key infrastructure (PKI) to deploy and manage digital certificates within your organization. ADCA is needed whenever you are hosting a web server […]
CUCM Upgradation and Migration takes an ample amount of planning and prerequisites check before actual migration and post-migration. In this article, we will discuss how the approach should be. Most of the environments are still running on 8.5 which is EOL and EOS (End of Service). To get back to pace, everyone must plan for […]
GLBP (Gateway Load Balancing Protocol) GLBP is a Cisco propriety protocol that only works on the Cisco component. This protocol is used to provide the High Availability (HA) for the LAN-connected users. Besides HA this protocol also provides Load balancing. In this blog, we will cover the below-mentioned points- GLBP Terminology GLBP Load-balancing Algorithm GLBP […]
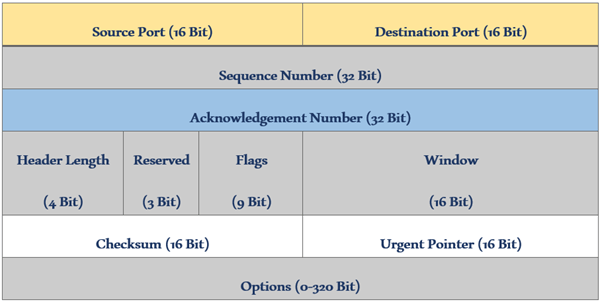
TCP (Transmission Control Protocol) is a reliable transport layer protocol that establishes a connection before sending data and it waits for a positive acknowledgment from the receiver. TCP is basically used where we want a guarantee of data delivery. It utilizes timeouts and retransmission to ensure error-free and sequenced data delivery. In our previous blog, […]
Hello friends! As I already said in my last blog on WSA integration with AD, we will discuss user authentication in this blog. To create group/user-based policies in WSA or user authentication for Internet access, we need to integrate WSA with AD. So, before reading this blog, please check out WSA, WSA Policies, and AD […]
There are quite a few OEMs in the VDI market these days. Big guns like Microsoft, Amazon, VMware, Citrix, and a few others have been in this segment for a while now. Citrix is one of the key players in the market if you talk about VDI. In fact, Citrix has constantly been securing its […]