Ethical Hacking involves attacking and trying to gain access to a computer, server, database, or application. Ethical hackers are also known as white hats, ethical hackers are security experts that perform these assessments. It helps to improve the security posture of an organization. There Are Mainly Five Steps In Hacking Reconnaissance The first step of […]
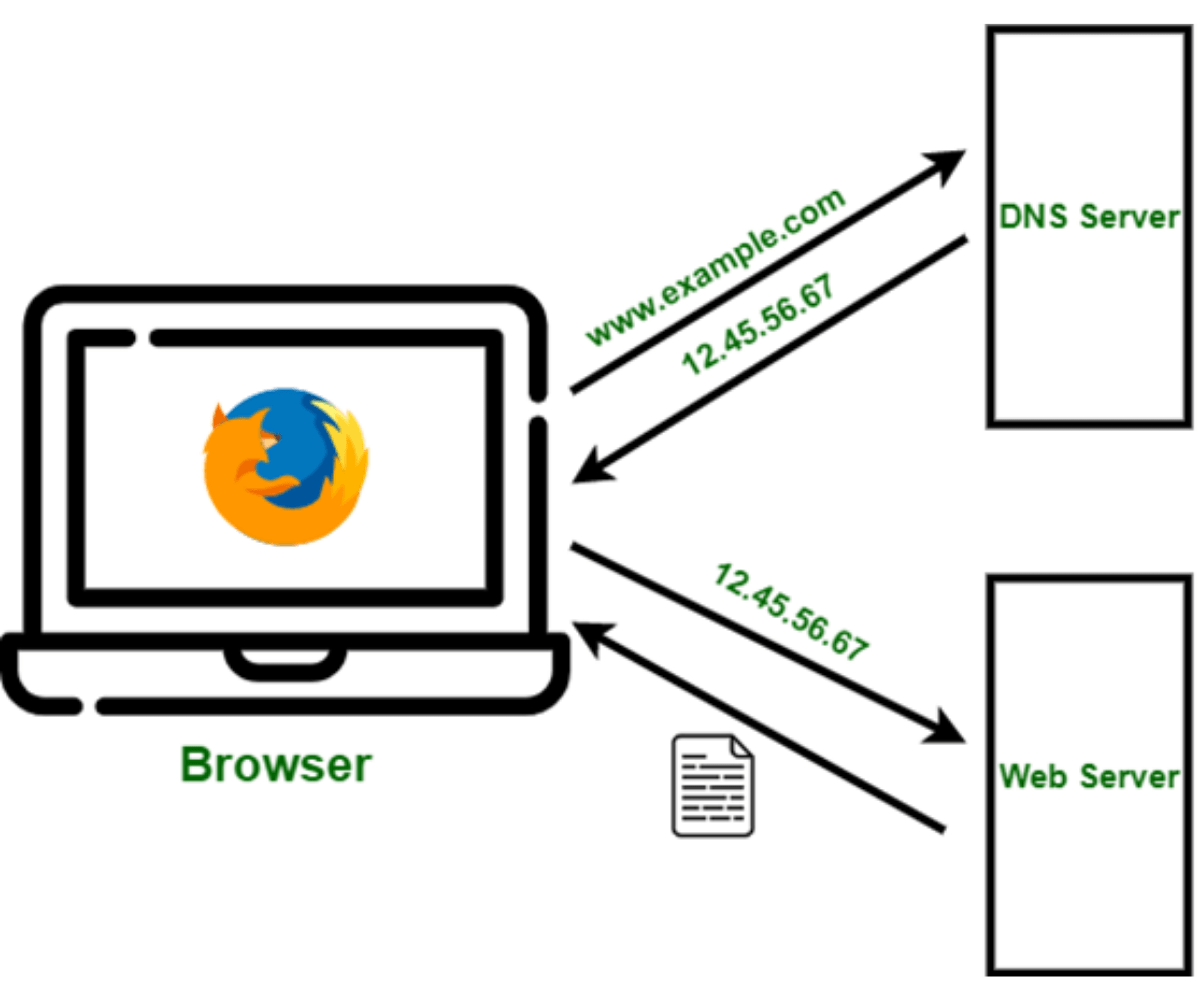
What is DNS? DNS translates domain names to IP addresses by which the browsers can load resources over the internet. Each device connected to the Internet has a unique IP address which is the identity to find other machines over the internet. DNS servers eliminate the need for humans to memorize IP addresses such as 192.168.1.1 (in […]
In this article, we are going to discuss MACSec & its role in our network environment. The following topics will be covered in this article: What is MACSec? Why MACSec as a solution? How MACSec works? Configuration of MACSec What is MACSec? MACSec stands for Media Access Control Security. It was introduced in 2006 […]
What is the blacklisting of an IP? A blacklist is a list of suspicious or malicious entities that should be denied access or running rights on a network or system. The blacklisting of IP addresses is a common occurrence on today’s internet. Most of us have encountered networking attacks in one form or another, ranging […]
In this blog, you will see about the necessary config. of NIPS 8350 (Network Intrusion Prevention System). We will give you point-to-point information, will not complicate this by going into deep theories. We will keep it technical for your better understanding. We are using hardened operating system Cisco Sourcefire NIPS-8350 physical device in this blog […]
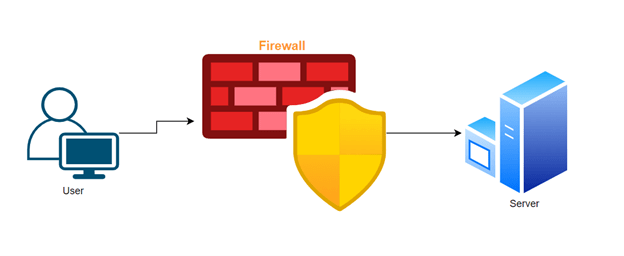
In this blog, we will discuss the fundamentals of Firewall services introduced in CentOS named FirewallD. Firewalld provides a way to configure dynamic firewall rules in Linux that can be applied instantly, without the need for firewall restart and it supports D-BUS and zone concepts which mark configures easy. It comes with an extremely powerful […]
As we learn in the last blog Multicasts with PIM DM (Protocol Independent Dense Mode) in this blog we will learn why we need Sparse Mode in PIM. To understand this, we require PIM Dense mode disadvantages. One of the big disadvantages of Multicast DM is, multicast stream sends (Flood) to all PIM enables routers […]
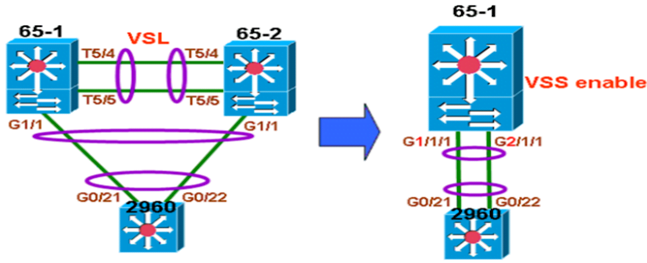
In this blog, we are going to talk about VSS and tell you how to configure the VSS in the live environment. We will see the prerequisite and limitations for configuring VSS first and then will come up with the VSS configuration. The following topics will be covered in this blog: Prerequisite for configuring VSS […]
What Is Nac? Network access control (NAC) is a solution that supports network visibility, access management through policy enforcement on devices and users of a corporate network. Why Do We Need Nac? In organizations now we have exponential growth of mobile devices and the endpoint that accessing their network and then they bring the security […]
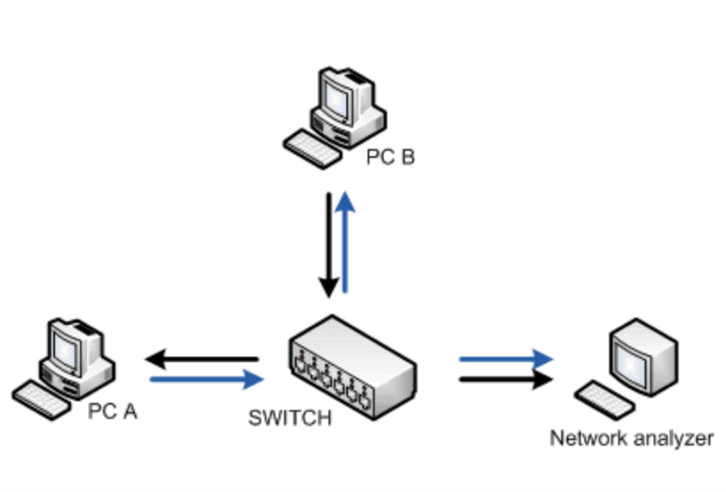
What is SPAN? SPAN stands for switchport analyzer .it is also called port mirroring. To analyze network traffic passing through the port by using span. How do SPAN works? It will send a copy of the traffic to another port on the switch. Span monitors received or sent (both) traffic on one or more source […]