What Are Different IT Risk Management Strategies?
Information technology or IT is no more a department that lies in a corner and does not impact day-to-day affairs. When you run an organization then you are involved in almost every sector and usually, they carry risks. IT risk management is a part of managed services for small businesses which are delivered by an IT consulting company. Every organization leads to IT challenges, and they can be small or big but how can we mitigate them?
What Are The Unique Challenges That Are Faced In IT?
Risk management is important as IT has become an integral part of our day-to-day and professional aspects. So, as a part of our lives, we need to mitigate the arising risks. In an ongoing project, there are many risks that can bring a temporary halt to the process. There are different and unique scenarios thus different risks. Some of them are like if the hardware and software integrations can keep up with the ever-changing technologies.
IT risk management is the process of identifying, assessing, and controlling the risks associated with information technology systems and infrastructure. The goal of IT risk management is to minimize the negative impact that technology-related risks can have on an organization’s operations, financial position, reputation, and ability to achieve its objectives.
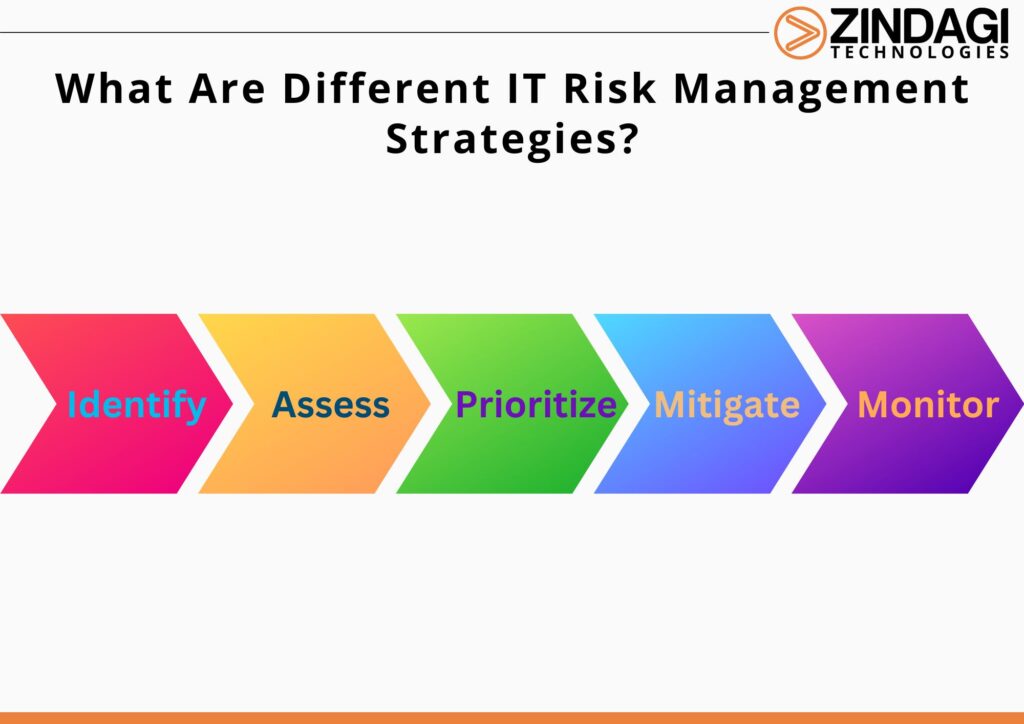
Here Are The Steps To IT Risk Management:
Risk identification
Identify the potential IT risks that could affect the organization, such as cyber-attacks, hardware or software failures, and data breaches.
Risk assessment
Evaluate the likelihood and potential impact of each identified risk. This involves estimating the probability of a risk occurring and the magnitude of its impact.
Risk prioritization
Prioritize the identified risks based on their likelihood and impact. This helps to focus resources on the risks that pose the greatest threat to the organization.
Risk mitigation
Develop and implement strategies to reduce the likelihood and/or impact of the identified risks. This may involve implementing security controls, such as firewalls and antivirus software, or developing contingency plans in case of system failures.
Risk monitoring
Continuously monitor the effectiveness of the risk management strategies and adjust them as necessary.
What Are The Different IT Risk Management Strategies?
The plan is to provide a stepwise approach that will identify, access and will manage the risks. Also, the process to regularly review and update the assessment.
Safeguarding
An avoiding strategy is when the company avoids the risks and focuses on resources at the end. Avoiding the risk is ok as it is no longer a threat but it has a downside as the potential return of the risk and not being able to avoid it is seen. So it should not be taken lightly.
Transferring the risk
When a firm transfers the risk to another entity, it is using a transference approach. This redistribution may be made to the employees of the corporation, a third party, or an insurance policy.
Reducing the impact
This is a risk mitigation approach in which the business uses whatever methods, teams, or resources at its disposal to try to lessen the effect of the risk. Little modifications may be necessary, but there must always be a method and a strategy.
Acceptance
This is a valid technique since it acknowledges that there is risk and prepares you to deal with it when and if it arises. Even though it’s occasionally unavoidable, if you’ve followed the instructions in your project risk assessment form, you can handle this.
We offer the best risk management as a part of our managed IT services. Having years of experience in managed it services, we have been handling many projects in public, private and government fields and giving out our best resources. Zindagi technologies are the leading and the top managed IT service provider company and will help you reframe your IT infrastructure. Drop us a message at 9773973971 or you can also email us to get in touch with us.
Author
Shweta
Senior Executive, S&M
