CISCO Stealthwatch-Secure The Multi-Cloud Networks
Covid -19 brought a temporary halt to seamless workflow and made people shift their work from home and to places that are safe. The travel was cut down to a minimum and working from home was an initial challenge. There was a good side too like being comfortable while working and giving more hours of hard work. While the drawbacks were more towards the security of the leaks that is a possible threat. Some of the conglomerates are still working with the risk of data leak as they are in work from home position.
Not every organization is completely equipped with all the tools and systems against cybercriminals. Lack of equipment, tools, solutions that will monitor the footprints of the network makes the organizations prone to cyber leaks. Just like evil eye protection is required to keep away bad vibes from attacking, similarly, protection from cybercriminals is also important. As the company grows and expands, it tends to have many blind spots that are the favorite spots of cyber attackers. If only once, the attacker seems to find the spot then they will pull out as much information as they want.
CISCO Stealthwatch – The One Stop Solution To Secure Multicloud Network
If you think that your company needs tools and systems that will stop the attacks and leaks, then you will first have to install them, and this might cost you a lot. What if we say that you can make full use of your infrastructure investments and are still able to provide the solutions to all the threats. CISCO Stealthwatch is the right solution that will not only make your business grow but will provide a solution to keep a watch on the people who are after your data.
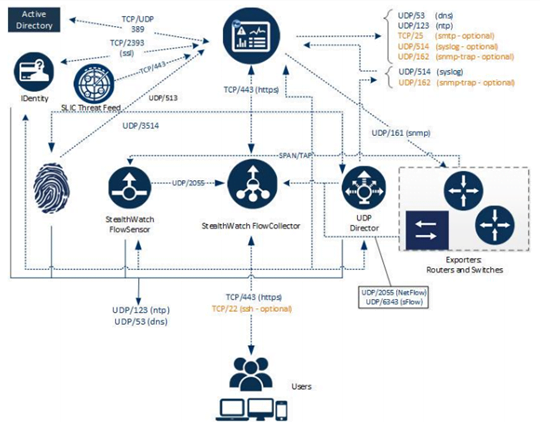
CISCO Stealthwatch will let you keep a watch on the network security traffic analytics and threat visibility with core insights on the complete network. On a higher level, three components are used by Stealthwatch for a seamless performance and protection from possible attacks.
Behavior Model
All the tasks on all the devices will be monitored under a watchful eye. After the report is generated then they will keep that report as a baseline so that the information reaches as soon as the change in the activity baseline is seen.
Multilayered Machine Learning
A multilayered machine learning will be deployed to look out for any advance threats and any malicious transmissions. Next, integration with a cloud-based multistage machine learning is seen which then connects the behaviors of the threats in the network.
Threat Intelligence
The data of the existing threats are present in Stealthwatch. Powered by the Cisco Talos Intelligence Platform, it is one of the best components of Stealthwatch. The information of IPs, domains, or any new malware or maps is gathered by Talos which gives an alert to GTI (Global Threat Intelligence). The best part is that the data is continuously updated for quick detection of threats. This in turn gives a faster response time so the threats can be handled.
Stealthwatch is the correct solution that provides the best security analysis and solutions. It will secure your network globally and you can continue the same infrastructure of your organization.
Zindagi Technologies has a team of experts in security, and they will help you in choosing the right solution so that you can make the most of it. Our security experts will provide the right future road map. So you have complete visibility, and add-on features that you can apply to your business. Call us on +91 9773973971 or get in touch with us to get started.
Author
Shweta
Senior Content Writer.
