How to Achieve Gateway High Availability with HSRP, VRRP, and GLBP Protocols Part-3
GLBP (Gateway Load Balancing Protocol)
GLBP is a Cisco propriety protocol that only works on the Cisco component. This protocol is used to provide the High Availability (HA) for the LAN-connected users. Besides HA this protocol also provides Load balancing. In this blog, we will cover the below-mentioned points-
- GLBP Terminology
- GLBP Load-balancing Algorithm
- GLBP Authentication
- GLBP Trace objects
- GLBP Configuration
Similar protocol HSRP and VRRP also using for Gateway High Availability, but do not provide the Load balancing. Read more about HSRP & VRRP to have better clarity.
GLBP Terminology
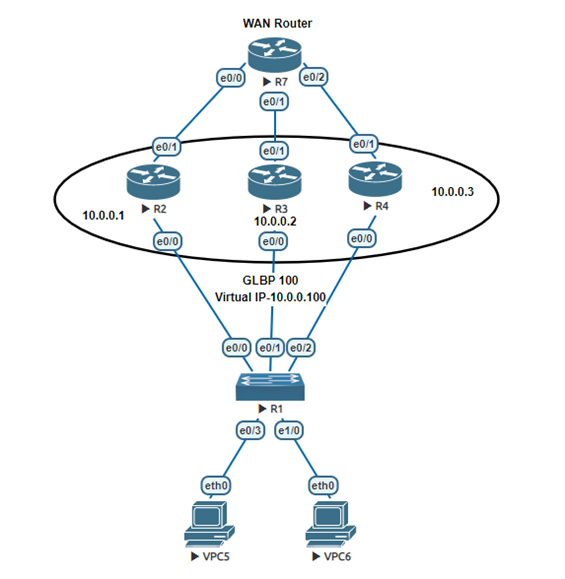
GLBP is similar to the HSRP protocol which works on single virtual gateway IP for multiple LAB users. In GLBP there is a concept of AVG (Active Virtual Gateway) & AVF (Active Virtual Forwarder).
AVG (Active Virtual Gateway)
AVG is responsible for responding the answer to all ARP (Address Resolution Protocol) which is requested for virtual IP Address. It is responding on the basis of the load-balancing algorithm on the requested ARP.
AVF (Active Virtual Forwarder)
AVF is responsible to forward the traffic which requests virtual MAC addresses.
- GLBP uses multicast IP 224.0.0.102 same as HSRP version 2.
- GLBP works on the application layer and using port number 3222.
- GLBP default priority is 100 same as HSRP, and priority can be 0 to 255 highest is preferable.
- In GLBP preemtion by default disable as HSRP, we can manually enable it.
- In GLBP for LAB users gateway will be the GLBP Virtual IP address.
- GLBP hello timer is 3 sec and hold timer is 10 sec.
GLBP Load Balancing Algorithm
GLBP uses the below-mentioned load balancing algorithm.
Round-robin load-balancing – GLBP by default use the Round-robin algorithm, in the Round-robin algorithm each router using MAC address in sequence to respond to the ARP request.
Weighted load-balancing – In this algorithm Router use configured weight to balance the traffic.
Host-dependent Load-balancing – In this algorithm host is always using the same router as assign.
GLBP Authentication
GLBP authentication can configure in two ways
- MD5 authentication– MD5 authentication is the most secure method to configure. The same key configuration will require, and the key will be sent in encrypted form.
- Plain text authentication- Plain text authentication is less secure than MD5. In this method, a password will be in plain text and it will be visible to all.
Tracking Objects
If ISP (Internet Service Provider) end interface or link will be down what will happen, still by default GLBP also sending the traffic to the active router as similar to HSRP. To prevent the black hole in the traffic, we need to trace the interface or link.
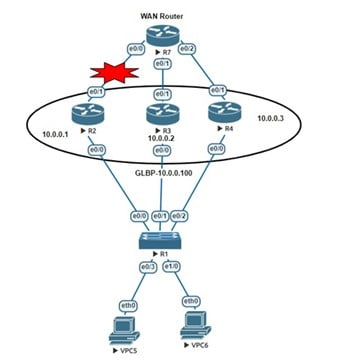
Here you can read about the trace interface configuration for GLBP.
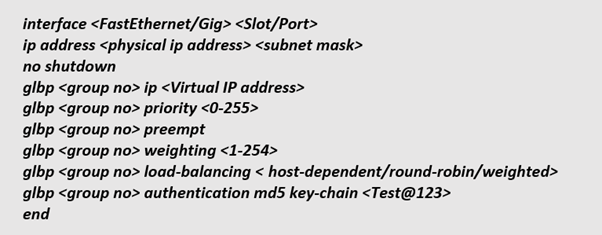
GLBP Configuration
From a GLBP configuration perspective keep in mind these configurations will happen on all those routers that will be part of GLBP. Kindly find the below configuration details-
Conclusion
To sum up we can say that this protocol provides gateway redundancy as well as Load-balancing between multiple links. But this protocol is Cisco propriety, and we cannot use it in other vendors’ devices. If we have other vendors’ devices, we can use VRRP and for load balancing, we can use Vlan based Load-balancing, like for some Vlans Router-1 will be active and for some others Vlans, Router-2 will be active. If you have any questions or want to share your views then you can get in touch with us or can visit our office. We have good experience in Data Center, IT Consulting, Managed IT Services, Cyber Security, Cloud Solutions, and many more. You can also give us a call on +91 9773973971.
Author
Brijesh Yadav
Network Consultant Engineer
