10 Steps to 802.1X Bootstrap configuration of NAD box.
Before we begin the 802.1X bootstrap configuration, we must first grasp two other terms.
If an end-user and the services that run on that end-user workstation/laptop are referred to as supplicant, you can execute the EAPoL massages and then enter the username and password for the user. Dot1x authentication refers to this type of thinking.
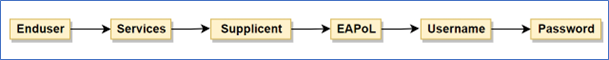
Note: – The end-user where the wired auto services are running that end user is going to call as a supplicant.
So, whenever you see 802.1X authentication means 100% a supplicant is running with username and password.
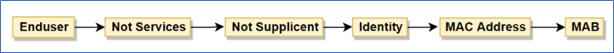
When an end-user isn’t running any services, which implies he isn’t a supplicant, his identity will be used as the MAC Address, and this kind of authentication is referred to as MAB.
Now the configuration of NAD BOX – 802.1X Bootstrap configuration
We’ll break down the NAD Configuration into ten simple steps.
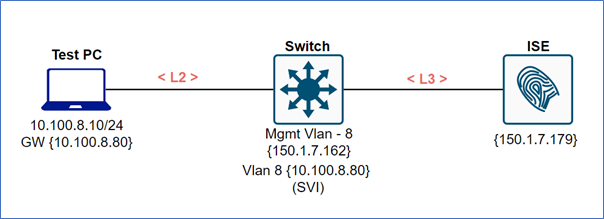
But first, let’s look at the image below using this example, and then we’ll go through all 10 steps with configuration commands.
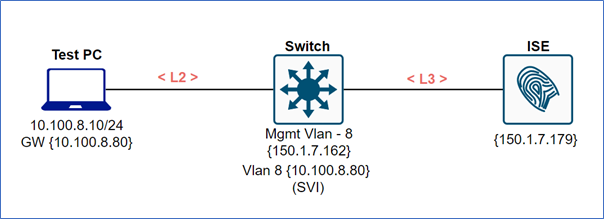
We will take an example of the above image IPs, VLANs, etc in the below commands.
Step – 1
Define the VLAN
#Vlan 8
#Desc data
#Vlan 1
#Desc MGMT
Step – 2
Creating the SVI
#Int vlan 1
#Ip address 150.1.7.162
#No Sh
#Interface Vlan 8
#IP add 10.100.8.80
#No sh
Step – 3
Enable AAA on the BOX
#AAA new-model
Step – 4
Define the AAA Server with the protocol.
#Radius server ISE-P
#Address IPv6 150.1.7.178 auth-port 1812 act-port 1813
#Key Cisco
Ip want to add secondary or tertiary ISE server
#Radius server ISE-S
#Add IPv4 150.1.7.180 auth-port 1812 act-port 1813
#Key Cisco
And—->>For Device admin
#Tacacs server ISE-P
#Address IPv4 150.1.7.179
#Key Cisco
Step – 5
Group the AAA Server
#AAA group server radius ISE
#Server ISE-P
#Server ISE-S
#Server ISE-T
Step – 6
Point out the AAA against this group
#AAA authentication dot1X default group ISE
Note: -In single mode deployment no need for “Group” (Group name) instead of Group use “RADIUS” after Group.
#aaa authorization network default group ISE
#aaa accounting update newinfo ……
Note: – Any current information on accounting send it to ISE
#AAA accounting Dot1X default start-Stop group ISE
Step – 7
RADIUS attribute, what RADIUS attribute need to define?
#Radius-server attribute 6 on-for-login auth
#Radius-server attribute 8 include-in-access-req
#Radius-server attribute 31 mac format ietf upper-case
#Radius-server attribute 31 send nas-port-detail
#Radius-server vsa send authentication
#Radius-server vsa send accounting
Note: –By default attribute number 1, 2, 4, 6 are enabled.
Username: -Attribute -1
Password: -Attribute -2
IP address of NAS: -Attribute -4
Service-Type: -Attribute -6
Step – 8
Define the three commands (Global commands)
#Ip routing
#Ip device tracking
#dot1X system-auth-control
Step -9
Define the source VLAN
# IP radius source-interface VLAN 1
Note: – Radius has two types of ports 1645/1646, these are the legacy ports numbers (Old port numbers)
ISE Can listen to both legacy as well as new port numbers (1812, 1813)
Step – 10
Configuration of the port
#Int gig 1/0/10
#Switch mode access
#Switch access VLAN 8
#Switch voice VLAN 100
Note: – Do we need to define VLAN?
VLAN 8 will be push by ISE, this is called authorization.
#Authentication host mode multi domain
#Authentication port-control auth
Or
#Authentication auto
#Authentication force-authorized
#Authentication force-unauthorized
To know more about force-authorized, unauthorized, and auto, read this blog Host Mode.
We here at Zindagi Technologies, have a team of certified Subject Matter Experts who specializes in SD-Access solutions, SD-WAN, ACI, and multiple technologies If you are looking for Planning / Designing / Implementation / PoC services for SD-Access and other technologies reach us at Zindagi Technologies Pvt. Ltd. Or drop us a WhatsApp on +91-9773973971.
Author
Ravi Kumar Singh
Consultant – Network Security
