What Is Netflow And How Can We Configure It On Cisco IOS?
NetFlow is a protocol developed by Cisco, used to collect metadata on Ip (Internet Protocol) traffic flows passing through a network device. A NetFlow-enabled device generates metadata at the interface level and forwards flow data information to a flow collector, where the flow records are stored to enable network traffic analytics and management.
A NetFlow-enabled device identifies a flow as a unidirectional stream of packets defined by its five tuples, a collection of 5 data points:
- Source IP Address
- Destination IP Address
- Source Port
- Destination Port
- Protocol
Flow identifies a communication channel with all packets sharing the same five fields belonging to the same flow.
How Does NetFlow Work?
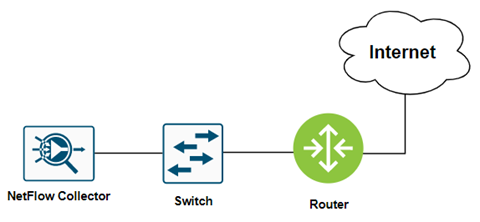
NetFlow follows a simple process of data collecting, sorting, and analysis. The main components include:
Ip Flow: Ip flow is a group of packets that contain the same Ip packet attributes. As a packet is forwarded within a router or switch, it is examined for a set of attributes.
Flow exporter: A NetFlow-enabled device that generates flow records and periodically exports them to a flow collector.
Flow collector: A server program responsible for receiving, storing, and pre-processing flow records received from NetFlow-enabled devices.
Flow analyzer: An analysis application that processes flow records collected by the flow collector into reports, alerts, and other interpreted results.
Why Use NetFlow?
NetFlow statistics are useful for several applications:
Network Monitoring: Businesses and users can utilize flow-based analysis techniques with NetFlow to visualize traffic patterns throughout the entire network. Also, NetFlow is used to analyze and profile a user’s utilization of network and application resources to detect any potential security or policy violations.
Security Analysis: Security predictive baseline analytics is arguably the most critical aspect of network management. By monitoring NetFlow, it’s easy to see where the most resources are being used. Many security attacks drain resources. So, if there are resource spikes in unusual areas, it can point to a security flaw.
NetFlow Configuration on Cisco IOS
The Following commands are required to enable NetFlow Export:
Switch(config)#ip flow-export destination <FlowCollector_IPAddress> 2055
Switch(config)#ip flow-export source <interface>
Switch(config)#ip flow-export version 9
Switch(config)#ip flow-cache timeout active 1
Switch(config)#ip flow-cache timeout inactive 15
Switch(config)#snmp-server ifindex persist
Enable NetFlow on each layer-3 interface to be monitored:
Switch(config)#interface <interface>
Switch(config-if)#ip flow ingress
Validate configuration
Switch#show ip cache flow
Switch#show ip flow export
Switch#show ip flow interface
Switch#show ip flow export template
Today, we learned the basics of NetFlow but there’s much more to it than just analyzing. Cisco’s Stealthwatch is the correct solution that works on NetFlow and provides the best security analysis and solutions. In the upcoming article, we’ll discover in-depth about Cisco’s Secure Network Analytics (Stealthwatch). Stay tuned with us. Want to read and learn more? Zindagi Insights is the place for you.
At Zindagi, our focus is to create value for our customers by applying our deep industry experience, technical expertise, and business intelligence. We are a top Managed IT services provider company and a leading cybersecurity company and we have the best resources that will help your IT infrastructure. Follow us on LinkedIn or contact us at 9773973971.
Author
Divyank Taneja
Associate Consultant
