3 WAYS BY WHICH MANAGED IT SERVICES WILL REDUCE DOWNTIME AND ENHANCE DATA COMPLIANCE.
The nature of today’s enterprises can be described as “always on the service,” which multiplies the use of the internet and the ability to contact clients 24 hours a day, seven days a week – these transformations in business today necessitate 100 percent up-time. Downtime during operating hours has a significant impact on customer service and productivity. Many corporate operations will come to a halt since firms and their consumers have become more reliant on technology to function, increasing the cost of downtime which can be reduced by Managed IT Services.

Gartner estimates that the cost of downtime per minute is $5,600. According to a survey by Information Technology Intelligence Consulting, a single hour of downtime costs more than $100,000. Hardware and software misconfigurations, equipment failure, human error, power outages, unfavourable environmental conditions, and cyberattacks are all common causes of downtime. Fortunately, many of these variables may be efficiently regulated and even prevented by using managed services.
Vulnerability and Penetration Testing – Managed IT Service
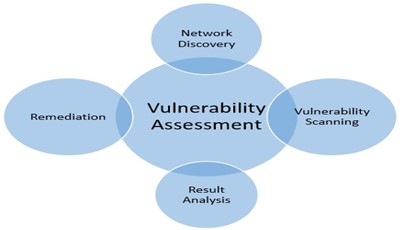
Vulnerability testing is the process of proactively discovering flaws in IT systems. Through simulated hacking assaults and software scans, technique vulnerabilities can be quickly identified and rectified. Although the testing method does not usually include a network-wide security assessment, it usually focuses on the perimeter and any flaws that hackers could exploit to get access to the systems without authorization.
Penetration testing is a regular occurrence that is frequently used to supplement a Web Application Firewall (WAF). The test comprises attempting to penetrate various application systems (e.g., APIs, front-end/back-end servers) to find vulnerabilities such as unsensitized inputs vulnerable to code injection attacks. The test’s findings can be utilized to improve the WAF security policies. Managed Services Providers (MSPs) assist firms in preventing cyber threats and enhancing uptime by employing these testing techniques.
Risk Assessment

Risk assessment provides firms with information about the risk profile of essential assets and systems, as well as procedures, policies, and controls. It also aids in the evaluation and mitigation of risks while exchanging information, particularly with third-party vendors, as well as the identification and mitigation of future dangers so that new technology can be integrated for improved security.
Endpoint Protection
Managed services also involve endpoint security. All a company’s network access points are protected with this solution. Because today’s businesses are increasingly implementing Bring Your Own Device (BYOD) rules that allow employees to work from any location, at any time, this managed services solution ensures that the network remains constant regardless of how employees work. Determining whether a network has been penetrated in any way is difficult, if not impossible, without this functionality.
The most important element to consider when choosing an MSP is its ability to meet your uptime requirements. By implementing rigorous standards and adopting best practices, the right MSP can help your company and systems be more resilient to downtime. As a result, the risk of human mistakes is decreased, reaction times are cut, and issues are resolved before end-users and customers are affected. Zindagi Technologies can undoubtedly meet all your managed IT requirements, allowing you to relax while we get to work.
Why should you take managed IT services from Zindagi Technologies?
Zindagi Technologies consults with you directly to determine your needs and then delivers you with the best cyber security, managed IT, Cloud Security, and IT consulting solutions available, allowing you to concentrate on other elements of your business. If you have a suspicion that you are being attacked or maybe attacked, please contact us right away so we can take care of managed IT services for your company. We can save your organization from all kinds of cyber threats and all you have to do is just drop a message at +91-9773973971 or even mail us if that is convenient for you.
Author
Esha Banerjee
Executive, S&M
