Deep Dive into SSL VPN Handshake Records
SSL VPN (Secure Socket Layer Virtual Private Network) is used for RA (remote access) VPN. Previously there was SSL Version 1, SSL Version 2, SSL Version 3, now we have TLS (Transport layer security) version 1.0, version 1.1 and version 1.2 are available. We can say that TLS is a successor of SSL. SSL and TLS are both cryptographic that provide authentication and data encryption between servers, machines, and application operation over a network. TLS uses port number 443 and TCP at the Transport layer.
Handshake Records
In SSL VPN all the massages are called records. We have the following handshake records:
– Client Hello Record
– Server Hello Record
– Server’s Identity Certificate Record
– Server Hello Done Record
– Client Key Exchange Record
– Change Cipher Spec Record
– Finished Record
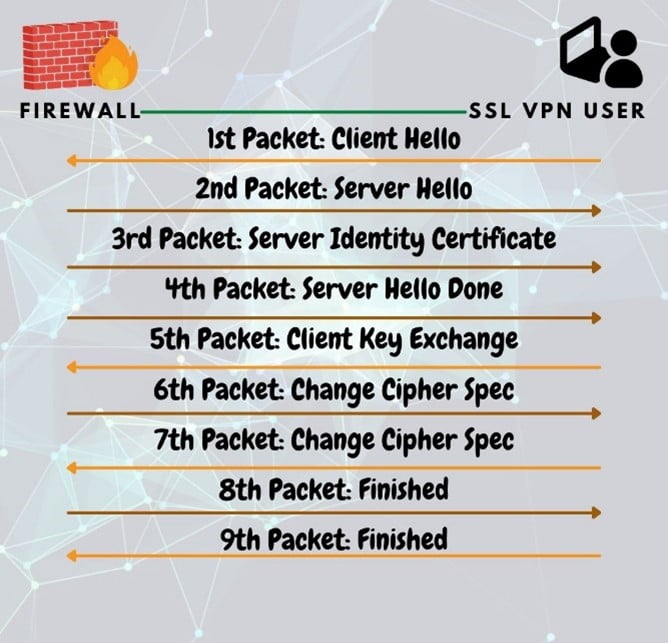
Client Hello
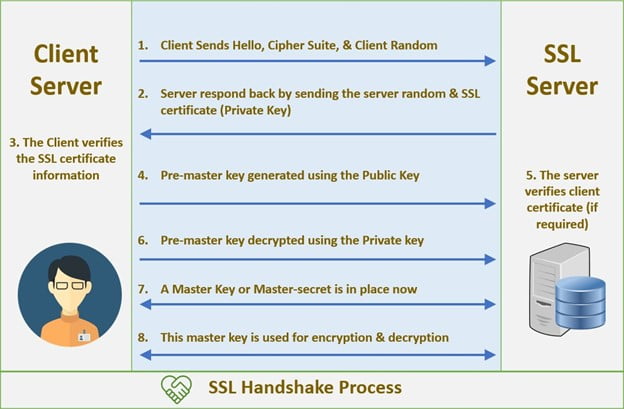
In client hello there will be a version field where a client will mention the SSL VPN version so that the server/ firewall can get the version information. There will be a session ID field where a client will set 0 for a new session and for the existing session client will set the particular value that was predefine by server/ firewall. The client will send the client hello first.
Server Hello
The server/ firewall will receive a client hello from a client then it will check the version and session ID, if the session ID is 0 then it will come to know that it is a new session request and it will set a session ID and send a server hello to the client. And if it will find any other value other than 0 then it will try to find that session entry in its database and if found then it will carry with that session ID otherwise it will set a new session ID and send the client and after that client will resend the client hello with a new session ID.
Served Identity Certificate
After sending the server hello server/ firewall will send its identity certificate. This identity certificate will contain issuer name (CA server), subject name (firewall/device), IP address, hostname, device type (e.g., firewall/router), location, organization name, validity (start date and end date), hashing algorithm, public key, etc. and also a digital signature of the issuer.
Server Hello Done
After that server hello done message will send by the server/ firewall in order to indicate the end of the server hello and associate messages.
Client Key Exchange
After receiving a server hello done message from the server/ firewall client will send a client key exchange message. The client will generate an RSA key and encrypt it by the server’s public key and sent it to the server and the server will receive this premaster key and decrypted it by its private key and make the master key.
The content of the client key exchange record will depend on the public key algorithm selected between client and server by their hello records. The client uses either premaster key encrypted by the RSA algorithm or DH (Diffie Hellman) for key agreement and authentication.
Change Cipher Spec Record
This message will send by both server and client in order to notify the receiving party that the subsequent records are protected under the most recently negotiated cipher spec and keys. Reception of this record causes the receiving party to copy the read pending state to the current state.
Finished Record
After Change cipher, the spec recordserver will send the finish message and the client will also reply with the finish message. This message will be encrypted and compressed under the current cipher spec in order to verify that the key exchange and authentication process is successful. After all negotiation and finished record, actual data communication will start. And these messages will be called application Records.
The above information will be useful for you. Additionally, we would like to say that we have highly qualified and experienced solutions architects at Zindagi Technologies who will help you to deploy Remote access VPN solutions as well as any other deployment in Enterprise Network, Data Center Network, Network Security, Cyber Security, Cloud & Virtualization domain. So, if you require us in the mentioned domains then please contact us at +919773973971.
Author
Dipayan Sarkar
Network Security Consultant
