Roles and Terminology for the SD-Access Fabric
The SD-Access solution is made possible by a combination of Cisco DNA Center, the Identity Services Engine (ISE), and fabric-enabled wired and wireless device platforms. The elements of a fabric site are created using wired and wireless device platforms. A fabric site is a node with its own control plane and edge node. A fabric-mode WLC is dedicated to the site for wireless, and an ISE Policy Service Node (PSN) is used for policy. To allow traffic to egress and ingress the fabric site, a fabric border node is necessary.
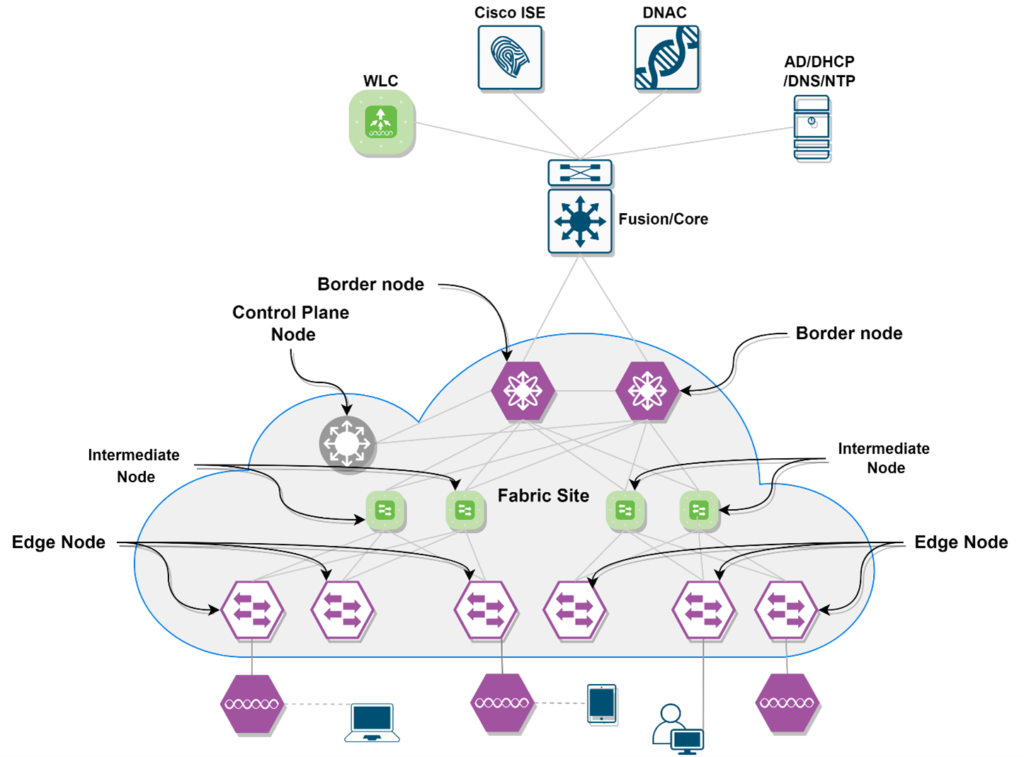
An SD-Access fabric role is a software construct that runs on physical hardware. A device can be configured to perform a single role or multiple roles. The best level of availability, resilience, deterministic convergence, and scale is achieved by separating roles onto separate devices.
SD-Access Fabric Roles
- Control Plane Node
- Border Node
- Edge Node
- Intermediate Node
- Extended Node
- Fabric WLC
- Fabric-Mode Access Point
- SD-Access Embedded Wireless
- Transit and Peer Networks
- Transit Control Plane Node
- Fabric Domain
- Fabric Site
- Fabric in a Box
Control Plane Node
Fabric CP is based on LISP Map-Server and Map-Resolver both functionality on the same box. It does
- Host Tracking Database. (HTDB)
- Endpoint identifier. (EID)
- Map-Server.
- Map-Resolver.
Host Tracking Database (HTDP): Endpoint ID to Routing Locator central repository (EID-to-RLOC), where the RLOC is the IP address of a fabric node’s Loopback 0 interface.
Endpoint identifier (EID): An endpoint identifier is an address that is used to number or identify a network endpoint device. MAC addresses, IPv4 addresses, and IPv6 addresses are examples.
Map-Server: Endpoint registrations with related RLOCs are received by the LISP Map-Server (MS), which is used to update the host tracking database (HTDB).
Map-Resolver: This informs the requesting device which fabric node an endpoint is connected to and, as a result, where traffic should be routed. The LISP Map-Resolver (MR) replies to fabric device queries for RLOC mapping information in the form of an EID-to-RLOC binding from the HTDB.
Border Node
The fabric border nodes act as a connection point between the SD-Access fabric site and the outside networks.
The following functions are implemented by border nodes.
EID subnets advertisement: The routing protocol BGP (Border Gateway Protocol) is used to advertise the coarse-aggregate endpoint prefix space outside of the fabric and vice versa.
Fabric Site exit point: The exterior border node is acting as the gateway of last resort, it uses the functionality of the LISP proxy tunnel router (PxTR) and there is an internal border that registers known routers with the Control plan node.
Network virtualization extension to external: Border nodes can do the network virtualization via using VRF-lite.
Policy mapping: The border node stores SGT information from within the fabric so that it can be properly maintained when exiting the fabric.
VxLAN encapsulation/de-encapsulation: The border node encapsulates packets received from outside the fabric and destined for an endpoint inside the fabric in fabric VXLAN. The border node de-encapsulates packets originating from within the fabric and destined for outside the fabric.
Edge Node
In a standard campus LAN design, the SD-Access fabric edge nodes replace the access layer switch. In LISP, the Ingress and Egress Tunnel Routers (xTR) are used to enable the edge node functionality.
Endpoint Registration: Edge node has an LISP CP session for all CP nodes. Once the host is onboarded and added to the Edge node-local EID-Table, then the edge node will send a registration request to the CP node for the newly added endpoint so the HTDP will be updated.
AAA Authenticator: The edge node collects authentication credentials from connected devices, relays them to the Authentication Server, (Eg. Cisco ISE), and enforces the authorization result as a part of the IEEE 802.1X port-based authentication process.
VxLAN encapsulation/de-encapsulation: Endpoint packets are encapsulated in fabric VXLAN and forwarded across the overlay, whether directly connected to an edge node or via an extended node or access point. Depending on the destination, traffic is routed to another edge node or to the border node.
Anycast L3 Gateway: The Anycast Layer 3 gateway is created on edge nodes as a Switched Virtual Interface (SVI) with a hard-coded MAC address that is the same for all edge nodes in a fabric site (Common Gateway).
Mapping of the user to virtual network: Endpoints are assigned to virtual networks by being assigned to a VLAN associated with an SVI that forwards traffic for a VRF. The Layer 2 and Layer 3 LISP VNIs, respectively, are made up of these.
Intermediate Node
Intermediate nodes are part of the Layer 3 network, which is used for connectivity between devices that operate in a fabric function, such as border nodes and edge nodes. The underlay network is connected to each other via the Global Routing Table.
Extended Node
SD-Access Extended Nodes allow an enterprise’s network to be extended by giving connectivity to non-carpeted areas of the business, known as extended Enterprise. This enables network access and control of IoT devices and devices in non-carpeted outdoor and non-carpeted locations like distribution centers, warehouses, and campus parking lots.
Extended nodes extend a fabric edge node’s Layer 2 port while also offering segmentation and group-based policies to the endpoints connected to these switches. Fabric-mode APs, E.g., can connect directly to the expanded node. Host onboarding is used to assign VLANs and SGTs as part of fabric provisioning.
Fabric WLC
AP image and configuration management, client session management, and mobility services are all provided by both fabric and non-fabric WLCs. Fabric WLCs provide additional fabric integration services, such as registering wireless client MAC addresses in the fabric control plane nodes’ host tracking database during wireless client join events and delivering fabric edge node RLOC-association updates to the HTDB during client roaming events.
Fabric enabled WLC does not receive data plain with CAPWAP tunnel, here CAPWAP tunnel only use for Control plain traffic, all the data plain encapsulated in VxLAN and send to Edge node and after that data is flowing like other wired traffic is following.
Fabric-Mode Access Point
Fabric APs are a type of wired host that is classified as unique. Edge nodes recognize APs as these wired hosts, apply appropriate port configurations, and assign the APs to a separate overlay network called INFRA VN using Cisco Discovery Protocol (CDP). Access points have their own EID-space and are registered with the control plane node as wired hosts.
SD-Access Embedded Wireless
The Cisco Catalyst 9800 Embedded Wireless Controller is a software package for Catalyst 9000 Series (Except Catalyst 9200 & 9200L) switches running in Install mode that enables wireless controller capability without a hardware WLC in distributed branches and small campuses. The embedded controller’s wireless control plane functions similarly to a hardware WLC.
The Cisco Catalyst 9800 Embedded Wireless Controller initiates CAPWAP tunnels on the APs and terminates them on the Cisco Catalyst 9800 Embedded Wireless Controller for controlling plane traffic.
The overlay traffic between the APs and the fabric edge node is encapsulated in VXLAN for the data plane traffic.
Transit and Peer Networks
Multiple fabric sites are connected by transits, also known as Transit/Peer Networks in Cisco DNA Center. There are two methods for transit connectivity.
- SD-Access based transit which connects to another SD-Access fabric site
- IP-Based transit Cisco DNAC supports BGP for IP Based transit networks, which connect to fusion and then the traditional world.
Transit Control Plane Node
SD-Access for Distributed Campus supports a fabric role design called transit control planes nodes. It functions similarly to a site-local control plane node, except it serves the entire fabric. when using SD-Access transits it requires transit control plane nodes to make communication possible in the entire domain.
Transit Control Plane has two functionalities.
- Site aggregate prefix registrations: it creates a central HTDB for all fabric sites.
- Control plane signaling: used to redirect traffic between the sites.
Fabric Domain
It’s a scope of an organization that includes various fabric sites and their transits. The idea behind a fabric domain is to group together on the screen different geographical segments of the network. So For example a network administrator can manger multiple fabric sites from one Screen/GUI.
Fabric Site
A fabric site is made up of a specific set of devices that operate in a fabric role, as well as the intermediate nodes that connect them. A fabric site must have a control plane node, an edge node, and a border node to allow communication to destinations outside of the fabric site.
As Cisco recommends, each fabric site has an associated WLC and perhaps an ISE Policy Service Node (PSN).
Fabric in a Box
Fabric in a Box is an SD-Access configuration in which the border, control plane, and edge nodes all run on the same fabric node. A single switch, a switch with hardware stacking, or a StackWise Virtual deployment are called Fabric in a Box.
These types of design have maximum supports max 200 endpoints. There is many more limitations of Fabric in a Box deployment we will discuss this in a separate blog in detail. At Zindagi Technologies, we have a team of certified Subject Matter Experts who specializes in SD-Access solutions. If you’re looking for Migration / Planning / Designing / Implementation / PoC services for SD-Access, reach out at Zindagi. Or call us at +91-9773973971.
Author
Ravi Kumar Singh
Consultant-Enterprise Networking
