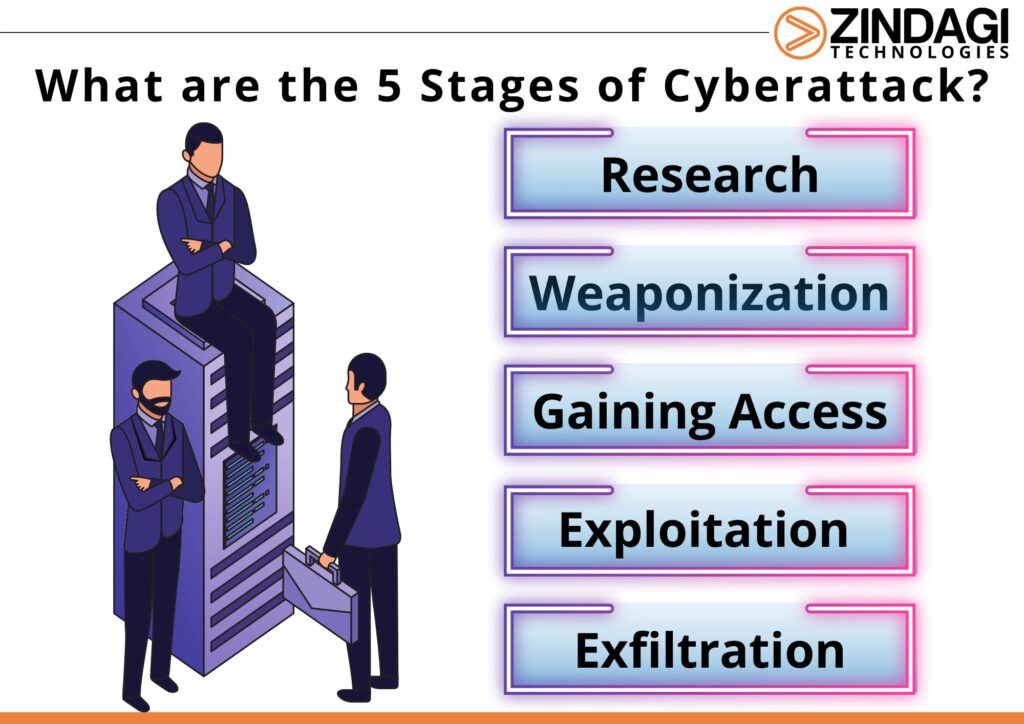
What Are The 5 Stages of Cyberattack?
It is said that if you have to catch the criminal then you have to think like them. In the scenario of a cyberattack, it does not happen in a jiffy, it takes planning and steps by which the systems and servers are hacked. It is important to know what and how a hacker thinks and how they will plan and execute. For this, an organization needs to have a Comprehensive Cyber Security Solution to keep its data safe.
Do you know about the average cost of hacking data? Gartner estimates that it falls between $3.86-$3.92 million. In industries like healthcare and finance, the cost would be higher but healthcare cost twice per record as compared to finance. The respective costs would be $429 per record and $210 per record.
Phase 1
Researching and Investigate
Footprinting is the preparation phase in which the hacker starts its research on the target and gathers as much information as possible. They want to know more about the target like who they are, where are they located, and what type of information the target has that can be stolen and is valuable. The type of attack will be planned accordingly as to how can they break the defence walls.
There are broadly 2 types of hacker investigation known as active and passive.
Active Reconnaissance
It happens sometimes that the attacker engages with the company that is on target. Getting to know the systems and people and gaining their trust. Port and network scanning so the hacker is able to see the architecture, firewalls, intrusion detections, or other security plans and implementations that are refraining the hacker to enter. Important information is revealed in this type of direct approach which will include the applications, operating systems, and some configurations that the organization has.
Network scanning
Data flow will let the hacker know about the network topologies of servers, firewalls, routers and hosts and with this, the active host will be determined. This will then be attached to the IP address. Port scanning will be the next step as the above steps will determine which machine to target.
Port scan
identifies the services that are accessible on the host ports of the target. There are several ways to do this, but the scan’s primary goal is to ascertain if the port is open, closed, or unresponsive. If a port is open, its answer will provide details that will allow an attacker to locate certain services that are hosted on the port, such as the application’s name and version and the operating system’s name and version. Versioning of the system name and configuration will provide an attacker with the knowledge they need to look for particular flaws or create new ones.
Passive Reconnaissance
This is the opposite of Active Reconnaissance as in passive, the information collected from open source. The target is not being engaged as the information comes from a free source. Information like system applications and the names of your employees.
Which open-source information is useful for hackers?
Job postings
This portal provides very basic information about the systems and applications that the company uses.
Social Media Presence
Some organizations post a lot about their company; mostly personal stuff like about the employees and what they do on daily basis. This gives a lot about their daily habits and a lot of information can be gathered.
WHOIS Lookups
This is one place where the hacker will definitely reach as this has information related to domain registration and IP address.
Public records can be accessed easily like tax records and this will give away the inner working of the company. In the case the hacker is targeting a publicly traded company then they will have the wealth information, annual reports, shareholders of the company, and other financial information. The need for a Comprehensive Cyber Security Solution increase here.
Emails
Harvesting emails is collecting email addresses by various collection methods, this also includes dark web purchases, directory attacks, or by commonly used email templates.
SERPs Queries
There are powerful web crawlers that index the internet and are deployed by Yahoo, Bing and Google. These are expansive web crawlers and with the right keywords and phrases down to the right punctuation, the hacker can gain access to protected login too.
Phase 2
Weaponize

After the completion of phase 1, phase 2 will begin in which the hacker would use different techniques to penetrate in the defense of the target getting to the desired information. The more skillful the hacker is the more information they will be able to get. Phishing emails would be drafted and watering holes or fake websites along with the developed malware ready to be launched. The exploitation of software and hardware is also researched and readied and after this, the attack commences.
Phase 3
Gaining Access

Various points can connect to a network. Employees who click on an attachment in a phishing email and download malware are examples of potential weak points. Other vulnerabilities might arise when staff members are persuaded to divulge sensitive information, such as login passwords, or when one of your systems is improperly set up or patched, allowing an attacker to get past the defences of your organization. It’s possible that the attacker used a sophisticated search engine query to locate a login page on the public web and then used data gleaned from social media and password-cracking tools to guess the username and password. They’re currently a part of your network.
Phase 4
Exploitation
Once the hacker is in the system then they go for two obvious steps known as escalating privileges and maintaining access. The hacker is able to install malware, a privilege that is normally blocked for any user. But this is used by the hacker through escalated services. there are 3 ways by which the access is gained by escalating privileges:
- Use of valid accounts
- Manipulating the access tokens
- Leveraging Windows UAC systems
The hacker will then manipulate the system to maintain access and will run the commands that will help them. Creating new user accounts, lowering the firewall defence, remote desktop access, backdoor entry, rootkit installation and other malicious files.
Phase 5
Exfiltration
Just like a thief will cover their tracks after committing the crime, the hacker will do the same. Once the infiltration is done, the process of exfiltration starts as the covering of tracks. This is done to make the detection difficult and, in some cases, law enforcement is also involved. Starting with uninstalling the programs and deleting any folders that were simultaneously created. The next step would be to delete the audit logs and modify or edit anything that makes it the same again.
So these were the 5 phases that a hacker follows to infiltrate the server of the system. Zindagi Technologies will provide you with end-to-end strategic assessment and support from the experienced team so even if this happens to you then it would be easy to mitigate it. Give us a call at +91-9773973971 or email us. To know more about our service and what we do, follow us on LinkedIn and stay updated.
Author
Shweta
Senior Executive, S&M
