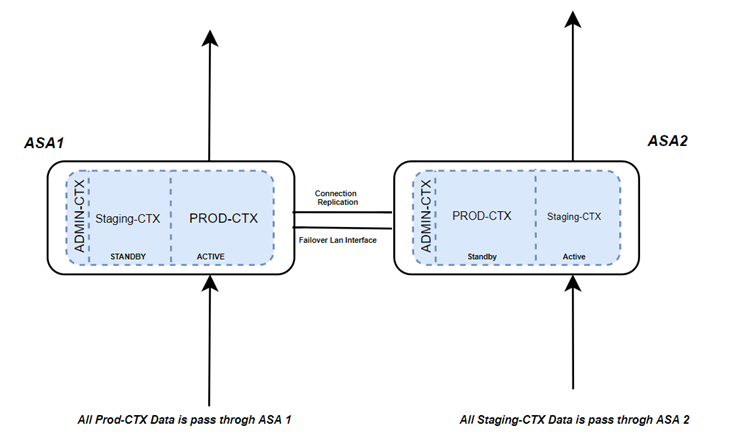
What is meant by a Fail-Over? How does it works on Cisco ASA? The meaning of the word “Fail-Over” is a procedure by which a system automatically transfers control to a duplicate system when it detects a fault or failure. In this blog, we will learn how Active-Active Failover works on Cisco ASA. So, when an ASA […]
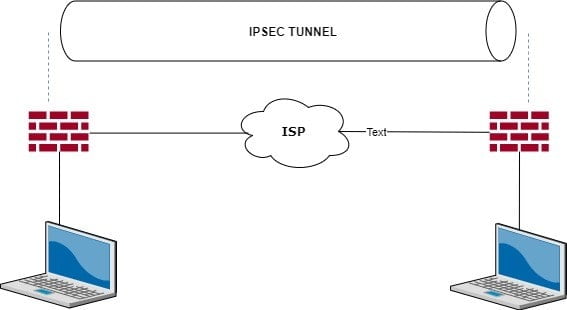
What is IPsec? IPsec VPN (internet protocol security) is a protocol or method to encrypt the traffic between two branches or sites. It is used to secure the traffic over an untrusted network, and we can understand by its name that it provides security of INSIDE network IPs. It provides Confidentiality, Integrity, and Authentication over […]
In this blog, we will learn about VLAN Trunking Protocol generally called VTP. We will see why VTP came into existence and will discuss how it works and where it can be deployed. For understanding, we will take some examples. Before VLAN trunking protocol (VTP), for creation, addition, deletion, renaming of VLAN, we must go […]
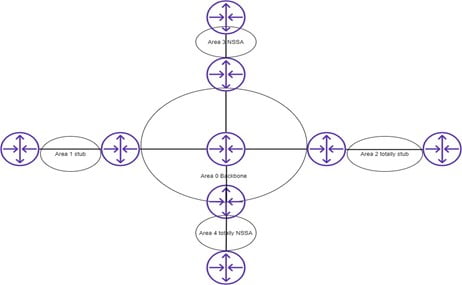
An Area type of ospf is a logical group of devices within a single administration. Cisco recommends that the single area should not have more than 50 routers. It has a 32 bit long ID and area-id can be represented in decimal number or ipv4 format Area type of ospf. WHY DO WE USE AREA […]
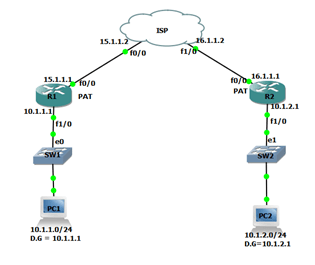
Communication between two private networks is not possible as the ISP is not aware of the private IP and moreover ACL is created on the ISP side which denies the private network. However, we can make communication possible with GRE. What is GRE? It stands for Generic Router Encapsulation. GRE is a Layer 3 Protocol. […]
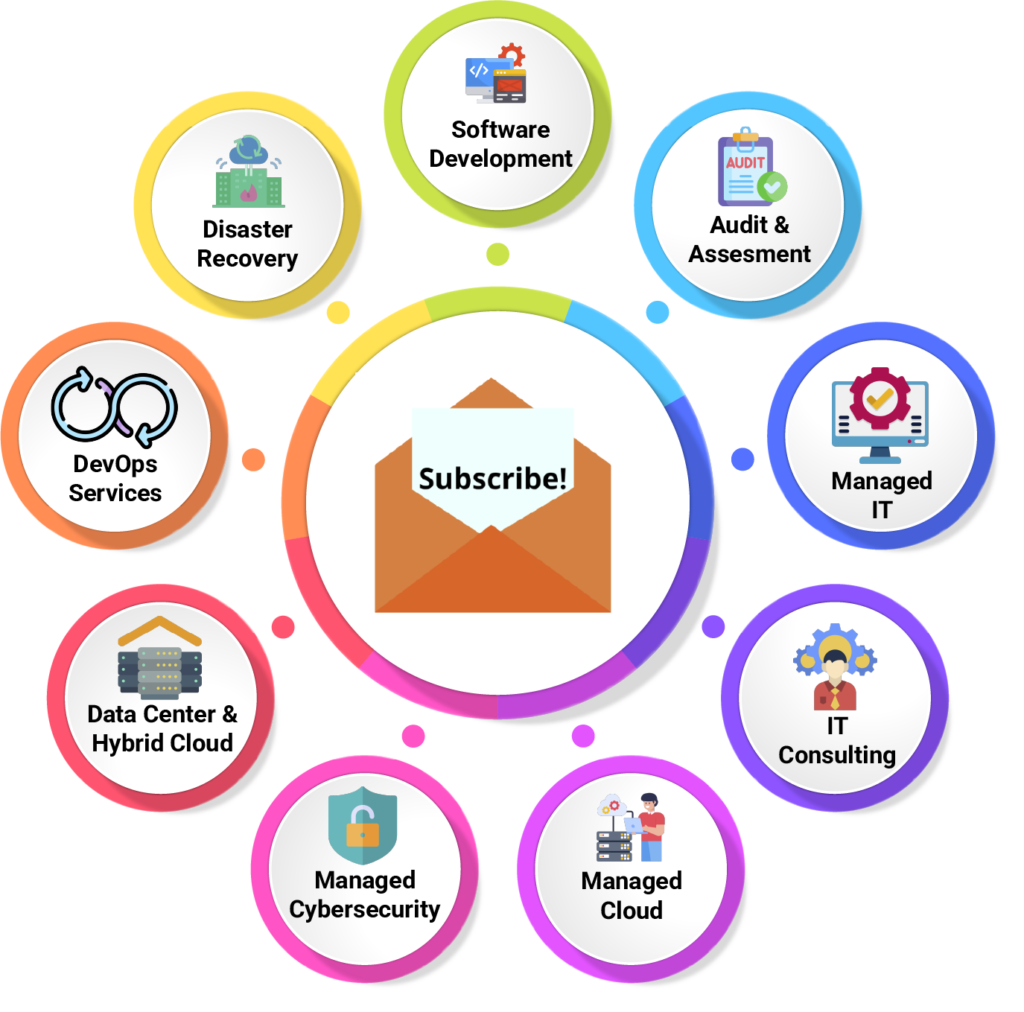
When running a business, it can be a daunting task to juggle different technologies and find effective solutions. Here at Zindagi Technologies Private Limited, we help our partners solve their unique challenges through innovative, integrated, and optimized solutions. We are a New Delhi-based technology partner that harnesses the power of business intelligence to serve our […]
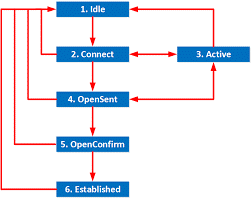
BGP Neighborship States And Attributes? Idle – neighbor shutdown/waiting for start 3-way handshake. Connect – try to connect TCP connection but won’t be confirmed. Active – TCP connection not completed, retrying to form tcp connection. Open-sent – TCP connection completed and sent the open message. Open-confirm – exchange open message, parameter agreed, send keep-alive after […]
What is Phishing? Phishing, which sounds similar to fishing, is a type of cyber security attack. In this, the hacker sends messages pretending to be a trusted person or entity and then they launch their attack to steal the data or valuable information. A phishing message is sent out to manipulate the victim in a […]
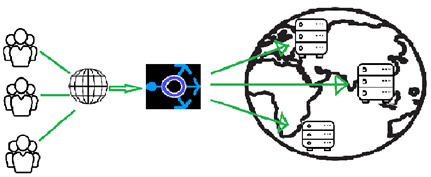
What is GSLB? Global Server Load Balancer (GSLB) enables balancing server traffic load across multiple physical sites. It Refers to web traffic management and application delivery over multiple data centers whether it is public or private clouds in multiple geographical areas. A load of hosted applications on the servers at each location is managed by […]
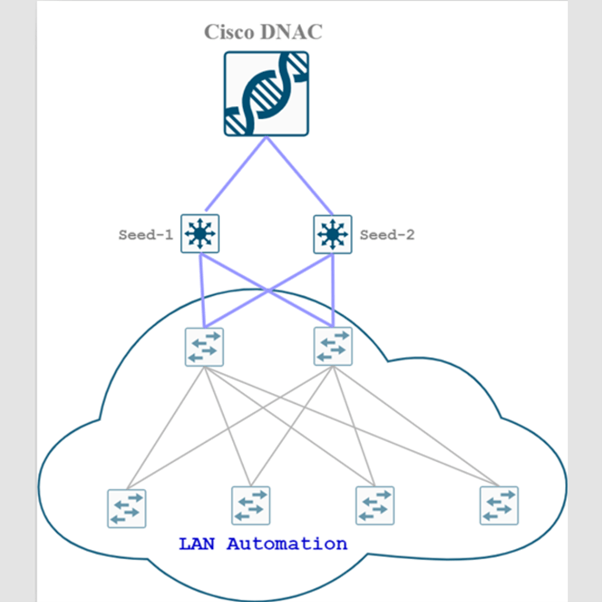
Cisco DNA Center has many features, out of them one feature is called ‘LAN Automation’ which I like the most. DNA-Center is designed to automatically discover and configure our underlay network that is called LAN automation in the SDA environment. LAN automation brings up the LAN network automatically starting from seed and peer devices. This […]