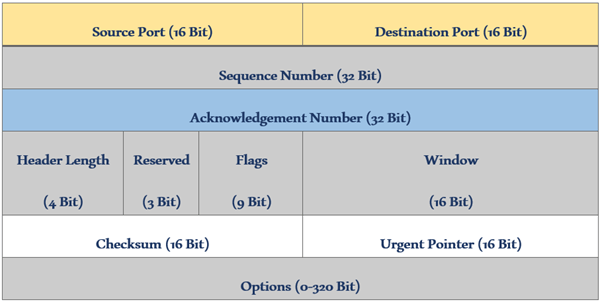
TCP (Transmission Control Protocol) is a reliable transport layer protocol that establishes a connection before sending data and it waits for a positive acknowledgment from the receiver. TCP is basically used where we want a guarantee of data delivery. It utilizes timeouts and retransmission to ensure error-free and sequenced data delivery. In our previous blog, […]
Hello friends! As I already said in my last blog on WSA integration with AD, we will discuss user authentication in this blog. To create group/user-based policies in WSA or user authentication for Internet access, we need to integrate WSA with AD. So, before reading this blog, please check out WSA, WSA Policies, and AD […]
In CentOS operating system, we manage all networking services with the help of the NetworkManager daemon. The Network Manager will also assist in configuring the control network devices and changing the network dynamically. It will help to manage the network connection status. In this blog we are going to understand CentOS NetworkManager daemon, installing, configuring, […]
There are quite a few OEMs in the VDI market these days. Big guns like Microsoft, Amazon, VMware, Citrix, and a few others have been in this segment for a while now. Citrix is one of the key players in the market if you talk about VDI. In fact, Citrix has constantly been securing its […]
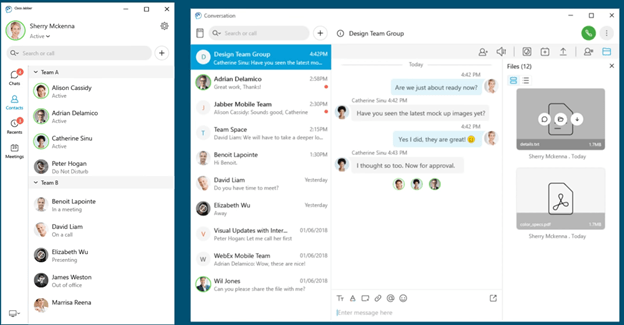
Jabber is a communication Software provided by Cisco. This Software includes Instant Messaging, and Voice and Video Communication. Jabber can be Installed from the App Store, Google Play store, and installed on your desktop Making easy use across all platforms. The main feature of Jabber is that it provides mobility, unlike hard phones. Moreover, it […]
As we learned in the previous blog on How to achieve Gateway High Availability with HSRP, VRRP, and GLBP Protocols Part-1 basic of HSRP (Hot Standby Router Protocol). In this Part-2 blog, we will learn HSRP in advance and the basics of VRRP (Virtual Router Redundancy Protocol). Concept wise VRRP is very similar to HSRP. We will cover the […]
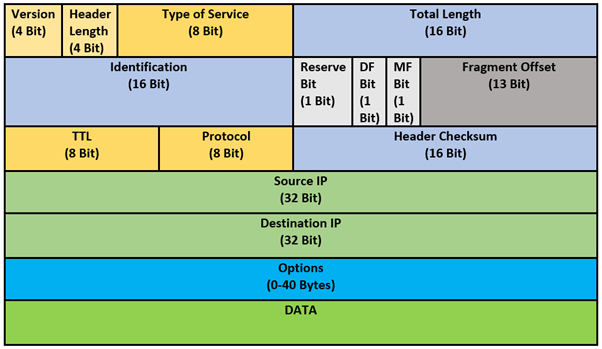
IP header is information that is attached with an IP packet at the beginning of it. The information in the header is used to transmit the packet to the defined destination. It can be 20-60 bytes in length. Every component/field in the header has its own significance. Let’s go through each component one by one. […]
In this article, we are going to discuss QoS & its significances. We will also discuss how QoS works. QoS stands for Quality of Service which is used to prioritize the traffic and reduce the packet loss, latency and manage lower jitter in our network environment. Before knowing how the user’s traffic gets prioritized while […]
Hi, today we are going to resolve all your doubts about WSA (Web Security Appliance) AD integration. I assume that you already know about the WSA (Web Security Appliance) and its policies. AD integration uses for user authentication in WSA. We are sorry to say that, today, we are not covering the authentication part in […]
In this blog we’re going to learn how to migrate a certificate authority server, A Microsoft certificate authority server to be specific. But before we look into how to migrate certificate authority from one server to another. Let’s first see what is a certificate authority server and why do we need it? A certificate authority […]