The recent pandemic showed us the importance of security one should have in their organization. The situation can change anytime, and one has to sit back in their home and work from there. This usually gives a bigger advantage to the hackers, and they find a loophole that will give them away to sneak in […]
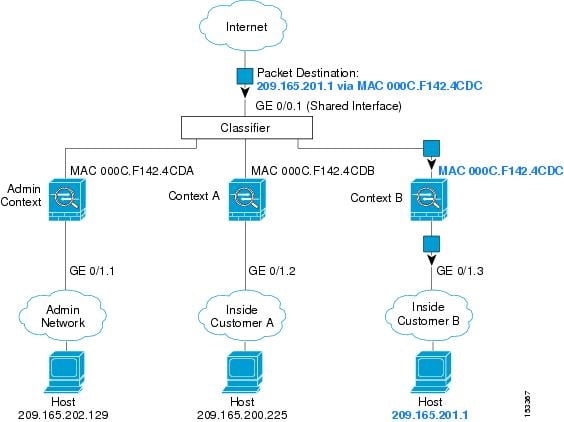
Network Security Engineer should provide security of communication and should be able to restrict access from insecure networks like the Internet. A Firewall is used for the restriction of any unwanted communication between any private and public networks. Now when we are moving towards Cloud, there is a requirement of multi-tenancy where you want to […]
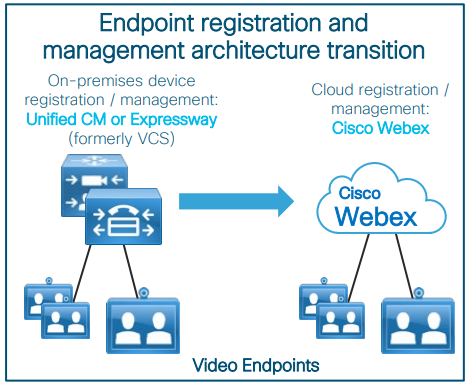
Cisco WebEx is a leading and Highly Secured Cloud platform that allows web, mobile, android, video endpoints to communicate via audio/video conferencing. While moving to Cloud Services, most of the organizations are still working on On-premises deployments with all endpoints registered UC platforms like Cisco Call Manager or VCS or TMS. The article will help […]
VMware is a leading software development organization in virtualization and cloud computing headquartered in Palo Alto, California, U.S. Founded in 1998 by Diane Greene, Mendel Rosenblum, Scott Devine, Ellen Wang, and Edouard Bugnion. Dell Technologies holds the highest percentage of equity shares in VMware since 2016. VMware Products And The Use Case VMware has developed […]
As we understand in the Part-1 blog “Improve our Monitoring systems with Cisco Prime Infrastructure Part-1” the importance of monitoring tools in network and basic installation process of Cisco Prime Infrastructure. Configuration, Maps, Services, Reports, Administration, Steps of taking backups, Steps to adding the devices, Licenses, set and create the reports, these all steps will […]
We hope you have got an understanding of the StackWise Virtual, its benefits, architecture, and the components from our previous blog. Now, if you want to deploy StackWise virtual in your IT environment then this blog will help you a lot in understanding the prerequisites, restrictions that should be kept in your mind before deploying […]
Remember Edward Snowden and how he leaked highly classified information from the NSA in the year 2013 when he was an employee of the CIA. The amount of information revealed by him was highly classified and being a government employee, this was a very serious offense. Now this was something that was “done” by a […]
In the first part of this blog, we have already discussed MPLS, its benefits, and the terminologies which are used in MPLS. In this article, we will continue with the remaining below pointers: i) MPLS Architecture & Packet Flowii) Several Applications used in MPLSiii) Prerequisite for Configuring MPLS MPLS Architecture & Packet Flow In the […]
Just like a drill, a number of corporate accounts are hacked, and the data is compromised. Most of the time, the corporates make only one change in the strictness and that is bringing out stricter policies and passwords. This is just like a false accomplishment that is short-lived in the sense of security. The result […]
Hi guys, we are here to dive into WSA (Web Security Appliance) Policies. You may be good or new to WSA but if you want to be a hero in WSA then we recommend this Blog. Please check it out. In this blog, we will talk about only the policies of WSA and from this, […]