Cloud is a place when you can store the data of the company and create a secure space. To manage a cloud in the self-mode is a tedious task that can distract you from your business strategies. If you have managed the cloud, then you won’t have to worry about the daily dedicated operations that […]
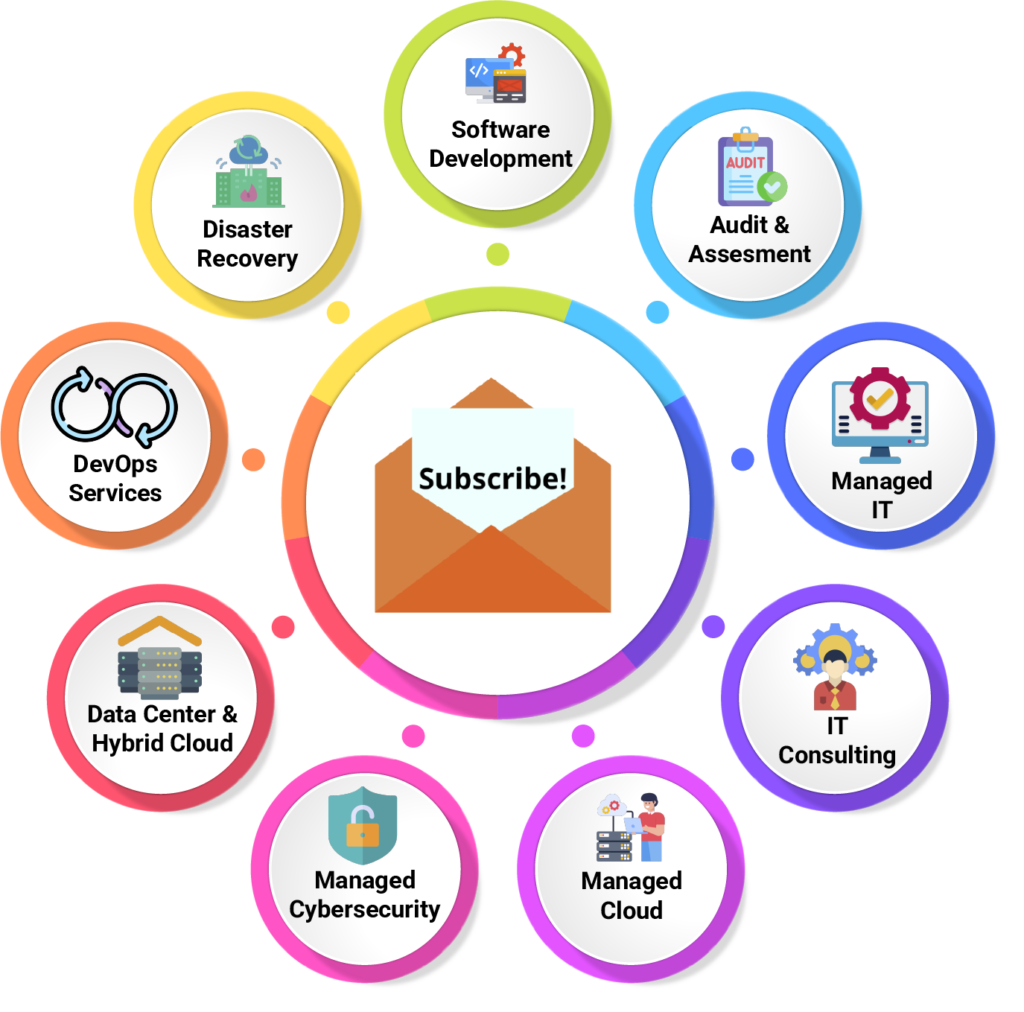
In our previous posts, we talked about the security advantages of Managed IT Services and the benefits managed IT provides, and how these factors contribute to the management and monitoring of a business to have improved stability, reduction, financial plan, security, and dependability. Getting back to the basics; it is better to know what types […]
In our day-to-day life, we have a best friend at home that is the Wi-Fi router because it gives you the Internet via LAN and as well as Wireless. We must secure our router because it is the only gate towards the internet and as well as towards your internal network. We connect our personal […]
There are a lot of ways in which managed IT services can be helpful in giving more time to your business. Monitoring the IT infrastructure and having it maintained by experts is much more effective rather hiring a separate IT director. Daily maintenance or having a dedicated team for timely follow-up will take a lot […]
After server 2012 editions, it will have a new feature called, “Deduplication Engine”. Server 2012 is also carrying this feature. In this blog, we will have look at how to configure the Deduplication feature in windows server 2019. It is not supported for certain volumes, such as any volume that is not an NTFS file […]
Managed IT Services means when an organization is giving third-party access to certain IT Functions. This is done so that the work does not stop, and the services are functional all the way from the bottom to the top. We also call it remote work management. There are circumstances when a team will remotely monitor […]
For everyone, having their own business is a proud moment in life. Setting up a business is not easy and running a business with complete hard work is equally difficult. When you are doing well in your work and having a good outcome then you might get exposed to cyberthreats. Not only your business is […]
There were times when we were concerned about the Wi-Fi speed on our weekdays or off days, but the pandemic showed us how important Wi-Fi is and the speed should always be good. When people switched to the “work from home” state then the only reliability was a GOOD WI-FI SIGNAL. This was a very […]
Our goal as Network Security Engineer is to be able to secure network access of endpoints connected over networks. E.g., Windows Desktop users connected to the office network switch. We have wired or/and wireless users in offices trying to connect to an office network or remote users connecting to an office network over an SSL […]
In the last blog, we covered the basic setup of the Cisco Meeting Server. In this blog, we will discuss CMS Cluster. In this article, we will cover Database Clustering, Call Bridge clustering, and XMPP Clustering. For database clustering, you require a minimum of 2 Cisco Meeting Servers or when you have at least 2 […]