What Is Man In The Middle Attack (MITM) And What Are Its Types? (2)
We all have heard the phrase “Sharing is Caring” but not in the case of your digital information which is to be kept personal. You don’t share your bank details, passwords, name, DOB, address, and other details with an unknown person. The hacker is that unknown person who plants himself in the middle of the conversation, server, IP, browser, and places that you can’t imagine, to derive the info.
In our last blog, we explained the Man in the middle attack and what are its types. We have already explained three types of MITM attacks namely DNS Spoofing, HTTPS Spoofing, and Man In The Browser (MITB).
In this blog, we will continue with SSL Stripping, Email Hijacking, Wi-Fi Eavesdropping, and Session Hacking.
SSL Stripping
This is also a type of MITM Attack where the hacker stages a stripping scheme of SSL against the victim. We already know that the HTTPS traffic cannot be broken but the hackers can downgrade the communication between the two parties in an unencrypted format. So when the victim tries to connect with the server the attacker gets in the way of the connection and establishes a connection with both. When the response is received from the server’s side, the attacker passes it on to the victim in an unencrypted manner making them think that they are talking to the legitimate party. Through this, the attacker is able to gather sensitive information and use it as per their needs.
Email Hijacking
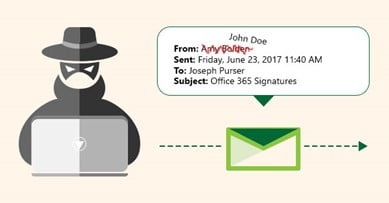
As the name suggests, email hijacking is a type of attack in which the attacker gains unauthorized access to the email to keep an eye on the exchange of conversation happening between both parties. You must have come across a malicious email that is asking for money to be transferred to your bank account as the funds are not sufficient. In such cases, the attacker might take over the email and the connected accounts with that email id. The email is hacked by directing the user to a bogus login page and forcing the user to reveal the credentials by which the hacker logs in himself. Another way is by the help of the keylogger malware as it is one of the many social engineered scams.
Remember what happened in 2016 when hackers managed to hack the email account of John Podesta and it gave a blow to Hillary Clinton’s campaign?
Wi-Fi Eavesdropping

This attack also goes by the name of the “Evil Twin”. In this type of attack, the hacker will create a wifi hotspot near a place where there is a public network available and most people are connecting to the same network. Later on, the name of the malicious wifi network will be changed to the name that is of the public wifi (thus the name evil twin). If a person is visiting a place where they are regular and their phone automatically connects with the wifi. They think that the wifi connection is the real one but it’s not, their phone gets connected with the malicious wifi. With that, all the information is being laid on a plate and served to the hacker.
Session Hijacking
Also known as cookie side jacking as it will give full access to the hacker. It happens when you sign in to any online account and the application gives a “session cookie” that gives access to the account after identifying the user. The server will enable the use of the application till the device of the user will hold the session token. After logging out the session token invalidates but the hackers steal the session token and steal the data. It can also b done with the help of malware that mirrors the inputs and steals the information.
This brings us to the end of the part two series. We hope that we made it simple to understand the 7 types of MITM attacks.
If your organization/public sector/private sector needs a great security option, then Zindagi Technologies will become your savior. Call us on +91 9773973971.
Author
Shweta
Senior Content Writer
