We will be continuing with our security point of view and this time we bring you a new blog on how you can prevent password attacks. In our previous blog, we discussed the issues of cybersecurity and how they can create havoc on the security of an organization. Let’s know something about passwords There is […]
Open web application security project (OWASP) is a non-profit organization that works with the goal of helping website owners and security experts to protect web applications from cyber-attacks. For the purpose to perform security assessments and research OWASP has more than 30,000 volunteers around the world. It represents a broad consensus about the most critical […]
Hello friends, today we will look at a very important part of Content security which is critical to a firm. We use DLP (Data Leak Prevention) to prevent data leakage and in this blog, we will work on Data Resolve inDefend DLP. The DLP (Data Leak Prevention) are of two types: – Endpoint DLP (Data […]
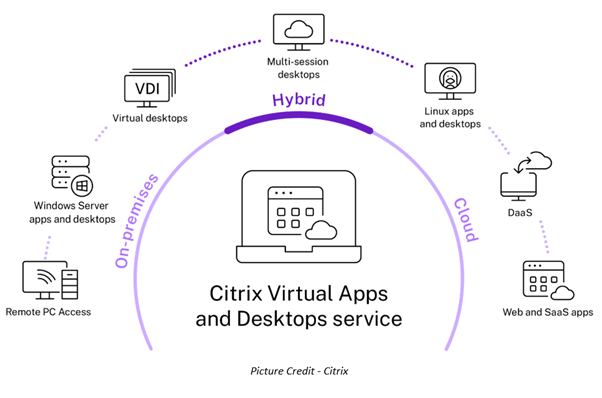
Citrix has been in the Virtual Desktop Infrastructure (VDI) line of business for ages and has been securing its place in the Leaders in Gartner’s Magic Quadrant for a very long time now. Citrix’s offering for Virtual Desktop Infrastructure is known as Citrix Virtual Apps & Desktops. Before we begin, if VDI happens to be […]
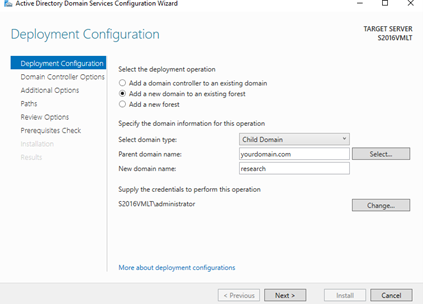
Extra AD domain controllers are not recommended because they are hard to administer. However, you may need an extra domain (Child domain controller) in the following scenarios. In this blog, we will explore adding a child domain to an existing forest. The Active Directory Domain Services (AD DS) design teams have finished the design phase […]
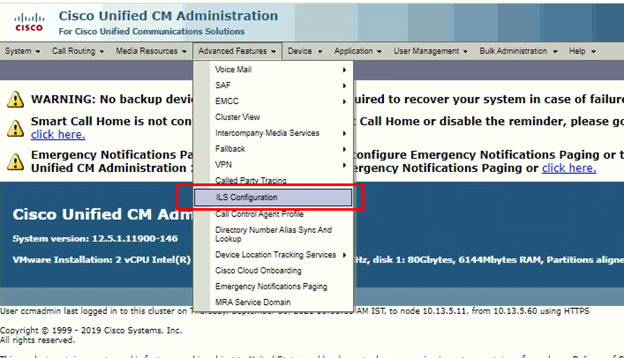
The ILS – Intercluster Lookup Service feature enables different CUCM Cluster to exchange directory URI with other clusters in an ILS network. URI Replication provides support for intercluster URI dialing. ILS runs as a service only on the Publisher node of a cluster. ILS works like Voice Routing Protocol because it behaves like a dynamic […]
According to CISCO, Cybersecurity means protecting systems, networks, and all digital platforms from cyber attacks that are harmful to your organization. Most people have a philosophy that if they will see something then only they will believe it. In cybersecurity, some things are different, if you see some attacks then it’s already too late to […]
Why VMware? VMware is the leading software development organization that developed multiple software’s for various data center needs and continuously developing innovative software’s to help the customers to modernize the traditional data center. VMware has acquired multiple software organizations to expand the product offerings, seamless integration, and provide scalable and efficient architecture under a single […]
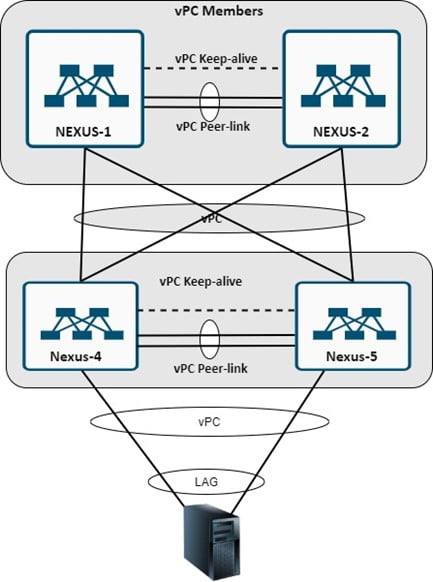
vPC (Virtual Port Channel) is the Cisco Proprietary feature that is only working on Cisco Nexus Components. vPC use to make Nexus devices logically single devices for the end host or devices. vPC is also known as Multi-chassis EtherChannel (MEC). vPC configured Nexus switch logically single for end-host/servers to traffic will be sent active-active from […]
An organization will work flawlessly when they have the best IT provider or managed IT services provider. But what if your IT provider is not giving what they promised? How will you ask them to cooperate, so they do what they have in SOW? Or is it time to switch the IT provider? What Signs […]